Cyber Security Skills Foundation Course

TAUGHT BY A MASTER - World-Renowned Cyber Security Expert and Instructor Kevin Cardwell.
Taught by world-renowned cyber security expert and instructor - Kevin Cardwell - CYRIN’s new Cyber Security Skills Foundation course is 40 hours, self-paced, and on demand. It's available 24/7 and integrated into CYRIN Labs – where, for the first time, you can practice what Kevin teaches.
KEVIN CARDWELL is considered an authority on information security and vulnerability assessments. He is a developer, author, and instructor in computer forensics and hacking courses world-wide.
He has conducted technical presentations at Black Hat USA, Hacker Halted, ISSA, and the TakeDownCon conferences as well as many others. He served as leader of a DoD Red Team with a 100% success rate of compromise. Now Kevin brings his expertise to CYRIN’s Cyber Security Skills Foundation Course.
Cyber Security Skills Foundation • Key Reasons to Attend
Course Objectives
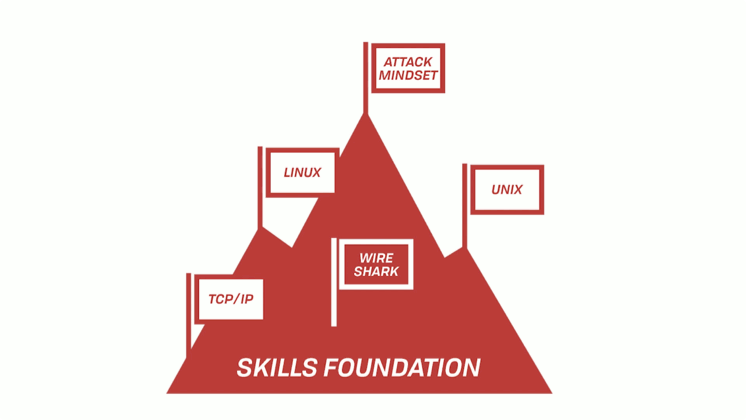
- Build a Solid Cyber Skills Foundation
- Explore the Power of TCP/IP
- Leverage Wireshark and perform protocol dissection
- Gain Familiarity with Unix and Linux
- Introduce the Concepts of the Hack and establish the “attack” mindset
Course Content
- Introduction to Core Skills for Effective IT Security
- TCP/IP 101
- Protocol Analysis
- Low Level Protocol Analysis
- Mastering Wireshark
- Unix and Linux
- Introduction to the Hacking Process

Who Should Attend
This course is for anyone who wants to start out with foundation and core concept skills for becoming a security professional.
Why Should You Attend
To gain the skills needed to move on to more advanced security training. Currently, a majority of professionals entering the field will lack the foundation that this course will provide.
What You Will Learn
- When you complete this course, you will have learned the foundations of security to include in-depth knowledge of the TCP/IP protocol.
- You will learn how to analyze packets for irregularities.
- You will learn how to detect signs of crafted packets.
- You will learn advanced protocol analysis techniques.
- You will perform low-level protocol analysis.
- You will learn functional skills in Unix and Linux.
- You will learn the fundamentals of vulnerability assessment and the hacking methodology.
What You Will Have at the End of This Course
- When you finish this course, you will have a solid security foundation in order to pursue more advanced security training.
- You will understand the mind of the attacker.
- You will have essential Unix and Linux survival skills that separate you from the many security professionals who are Windows centric.
Delivery
This course can be delivered in one of three ways. The first is an e-learning or self-paced environment where no instructor is involved. Should the subscriber choose this option, the course will be delivered via video instruction with pauses during this 5-day course for the students to complete the interactive keyboard CYRIN labs, exercises, and attack scenarios.
An instructor led course can be delivered in one of two ways. The first is online via Zoom or Google Hangouts or a similar platform where a live instructor manages a remote classroom environment. In this mode, the instructor leads students through the course with appropriate breaks where students complete assigned CYRIN interactive labs. Finally, the curriculum can be delivered in a traditional classroom setting where the students and the instructor are together in one physical location. In the current situation the last option is extremely limited. Contact us for details.
Kevin Cardwell's Courses on CYRIN
Cyber Security Skills Foundation
Gain the essential skills to build a solid security foundation. You will examine in detail the traffic that traverses the network at the packet and binary level. You will build solid knowledge on the lowest layers of the network. You will learn to master the TCP/IP protocol. You will learn essential UNIX and Linux survival skills that separate you from the many security professionals who are Windows-centric. Additionally, you will be introduced to vulnerability assessment and the hacking methodology. When you finish this course you will have a solid security foundation to pursue more advanced security training.
$1995 (1 year)

Essential Defense Tactics
Learn the foundations of security and defending architectures from attack. You will look at the concept of "thinking like a hacker" to learn techniques to defend from the types of attacks that are commonly conducted against IT/corporate networks as well as industrial control networks. You will learn powerful methods to analyze the risks inherent in your networks. Once your foundation has been set, you will look at the best practices and recommendations for reducing attack surface. You will also learn a systematic process for intrusion and malware analysis.
$1995 (1 year)

Advanced Defense
With this course, you can be among the few who transcend the old idea of the hacker having all the fun. Take pride being the defender, form an offensive mindset to skillfully orchestrate robust and solid defenses, and reinvent popular belief by beating the hacker at his own game. You will be evaluating advanced methods of defense fortification bringing you closer to establishing perfect security best practices and methodologies you can apply to your environments. This course teaches segmentation and isolation to reduce the effectiveness of advanced persistent threats.
$1995 (1 year)

Pricing
The price per student for each 5-day 40-hour course is $1995 where the course is delivered in an e-learning environment. The price per student for an instructor led session either online or in person is $3500 with a minimum of 6 students per class.
For special bulk and enterprise discounts, contact us directly or fill out the form below.


